Many initially associate multi-agent systems with simply using more prompts within a single workspace. However, discussions within the OpenClaw community reveal that effective multi-agent setups go far beyond this notion. Successful OpenClaw deployments demonstrate a paradigm shift towards separate services, each possessing distinct trust zones.
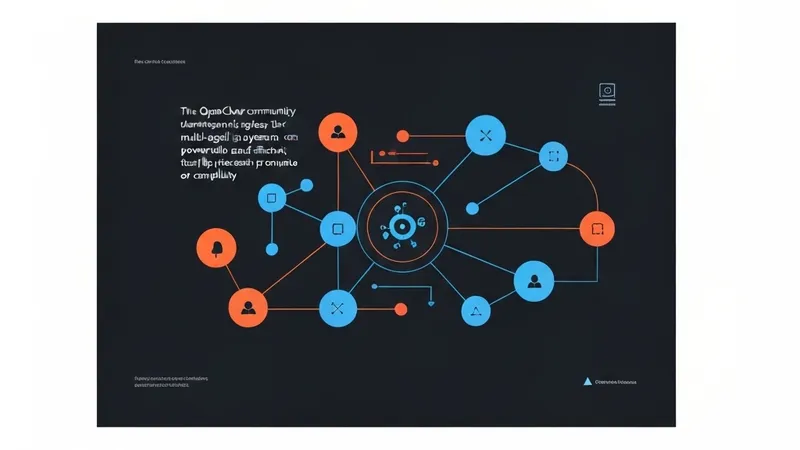
A recurring pattern involves specialized agents: a librarian agent, an executor agent, and a company-facing agent, typically interconnected via Agent-to-Agent (A2A) communication.
While seemingly a minor implementation detail, this distinction is profound. A separate prompt inside one workspace remains fundamentally one workspace, entailing: a singular context blob, a unified tool surface, a shared security boundary, and a common locus for bloat accumulation. In contrast, a separate OpenClaw instance introduces genuine architectural boundaries: distinct runtimes, isolated API keys, segregated networks, independent memory policies, and explicit handoffs. This fundamental separation marks the transition of multi-agent concepts from mere role-playing to robust system architecture.
A salient example emerged from an r/openclaw thread discussing an A2A plugin, vividly illustrating real-world applications: a sandboxed local OpenClaw communicating with a full-access cloud OpenClaw; a personal OpenClaw connecting to a company-wide OpenClaw for internal services; and teammate agents synchronizing plans over the internet to prevent conflicts. This goes beyond mere prompt organization; it represents genuine system design, addressing a common question from those attempting to confine multi-agent logic within a single workspace.
The fundamental reason to avoid consolidating everything into one OpenClaw workspace is that "the boundary is the point." When a librarian, executor, and company-facing assistant all reside in the same workspace, their supposed specialization becomes superficial. The librarian retains excessive visibility, the executor inherits undue context, and the company-facing assistant is merely one erroneous tool call away from accessing unauthorized resources.
The tradeoffs for different approaches are clear:
- Separate A2A services: Offer clear trust boundaries and can run on distinct machines or networks, but come with tangible setup and security overhead.
- Subagents within one OpenClaw workspace: Fast and simple with lower latency, yet provide weaker isolation of tools and context, and are more prone to bloat.
- n8n for orchestration coupled with agents for reasoning: Excellent for deterministic triggers and data movement, but the associated "glue code" can quickly become unmanageable.
My opinionated stance is that the complexity of multi-agent systems is only justified when the boundaries are genuinely real. If the division is merely "this prompt is the researcher" and "this prompt is the coder," then one likely doesn't have multiple agents, but rather a single agent wearing different name tags.
In the aforementioned A2A discussion, a commenter highlighted a pattern worth adopting: an agent designed to function as a librarian and gatekeeper for a Retrieval-Augmented Generation (RAG) implementation.