In distributed systems, the default state of agent trust is inherently broken. Consider a scenario where a payment agent on your network accepts POST requests to "/charge." It has no inherent way of knowing if that request originated from your legitimate order agent, a replayed token, or an entirely unauthorized source within your network. This is not a theoretical vulnerability; it represents a significant open door for security breaches.
Multi-agent e-commerce systems serve as prime examples where agent trust is paramount. Such systems typically involve:
- Payment Agent: Responsible for charges and refunds, posing a high-risk profile.
- Inventory Agent: Manages stock reservation and release, representing a medium-risk profile.
- Fulfillment Agent: Passes customer data to an LLM for shipping label creation and notifications, also a medium-risk profile.
Each of these agents becomes a liability if it accepts calls from an incorrect source or if there is no cryptographic record of the actions it approved.
What We're Building
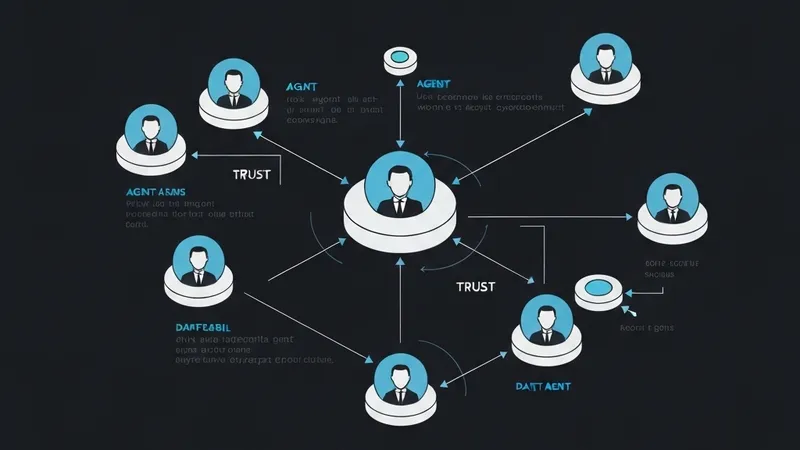
We are architecting a 4-agent order system fortified with cryptographic contracts between every pair of agents. This system comprises:
- Order Agent: Classifies inbound orders and routes them to the correct agent (Low Risk).
- Inventory Agent: Checks stock, reserves items, and triggers restocking (Medium Risk).
- Payment Agent: Handles charges, refunds, and reconciles transactions (High Risk).
- Fulfillment Agent: Creates shipping labels and notifies customers via an LLM (Medium Risk).
The core of this system's security lies in the requirement that every inter-agent call necessitates a signed contract. Without a valid contract, access is denied. Furthermore, these contracts cryptographically enforce scoped permissions, meaning an agent can only perform actions explicitly permitted by its contract.
Step 1: Register Agents and Issue Scoped Contracts
Each agent is provisioned with an Ed25519 keypair and a DID:key identity. Crucially, the scopes of their permissions are cryptographically bound, not merely configurable values that can be altered at runtime.
This initial step involves:
- Agent Registration: Each agent (e.g., order-agent, inventory-agent, payment-agent, fulfillment-agent) is registered, typically generating keypairs server-side.
- Contract Issuance: Contracts are then issued between agent pairs. For instance, a contract between the order agent and the inventory agent would explicitly define scopes such as "inventory:reserve," "inventory:release," and "inventory:check," along with a time-to-live (TTL).
- Granular Permission Control: A critical aspect is the fine-grained control demonstrated by issuing a contract from the order agent to the payment agent with a scope like "payment:charge:max_10000usd," deliberately excluding a "refund" scope. This highlights that a separate contract, specifically granting refund capabilities, would be required for such operations, ensuring strict adherence to the principle of least privilege and separation of concerns.
Through this methodology, the system ensures that even within an internal network, inter-agent communication is founded on cryptographic proof and the principle of least privilege, significantly enhancing overall system security.